
Simply password-protecting your Linux server no longer cuts it (they’re vulnerable to online and offline brute force and dictionary attacks, and people historically are terrible with maintaining secure password practices): you have to secure it with SSH keys. This tutorial will teach you what are SSH keys and how to replace the default Linux password authentication with SSH key-based authentication.
Note that I use a Contabo VPS in this tutorial, but this guide applies to any virtual server from any other provider. Also, I’ve included both a step-by-step video guide and written tutorial.
What are SSH Keys?
SSH keys are an abbreviation of Secure Shell keys. Cybersecurity researcher Tatu Ylönen created SSH in 1995, and they now come with every Unix, Linux, and Mac computer. They’re also available for every platform, and are a critical part of all cloud infrastructure.
How to Use SSH Keys for VPS Video Tutorial
Why Should I Use SSH Keys Instead of Passwords?
“Real deal Holyfield” hackers can crack your server’s password well before you finish skimming this sentence (PSA: always use a password manager like Bitwarden to keep your passwords secure). Hackers can use tried-and-true brute force attacks to get into your server, or other, more sophisticated methods.
Now, we’re not here to lecture you on security hygiene or best practices (you’re more than welcome to read scaremongering articles that have the eyeroll-inducing stock photo of a “hacker in a hoodie”). But, we do want to emphasize that SSH keys are the way to go for securing your server because much longer and more complex than any password could be. And unlike passwords, SSH keys aren’t sent to the server. You do have to protect your SSH key with a passphrase, though.
How to Generate SSH Keys
SSH uses pre-generated public and private keys (hence it being called a SSH key pair). These public and private keys are formed through asymmetric key cryptography, and they’re stored for future use. As a best practice, we recommend generating new keys for new devices (it’s more secure), but it does require re-establishing trust relationships.
How to Authenticate SSH Keys
The public key is saved on your server, while the private key is saved on your computer. If you try to log in to your server, the server will generate a random string and encrypt it using the public key. You can decrypt the string using the private key (this is the only way to decrypt the string).
The server then sends this encrypted string to your computer. Your computer will decrypt it with the private key and send the decrypted string back to the server. You can access your server if the decrypted string from your computer matches the original string from the server.
How to Generate SSH Keys for Linux
Open a terminal and enter the following command to generate a pair of keys (assuming your local computer runs Linux):ssh-keygen -t rsa
Note: you might need to choose a filename and file save destination depending on your version of Linux.
And here’s the default path for the saved keys:
/root/.ssh
While id_rsa is your private key, id_rsa.pub is your public key.
How to Generate SSH Keys for Windows
If your local computer runs Windows, we recommend installing PuTTY, the free and open source SSH and terminal emulator (it also includes PuTTYgen).
After installing PuTTY, open the Windows search bar and search for “PuTTYgen”.
After opening it, this screen will appear:
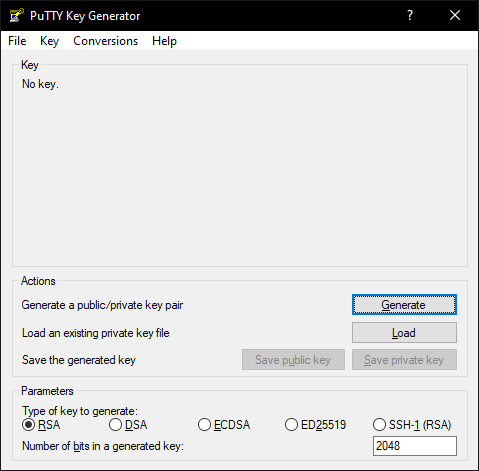
Just click on “Generate” and move your mouse over the blank field.
Your keys will then generate:
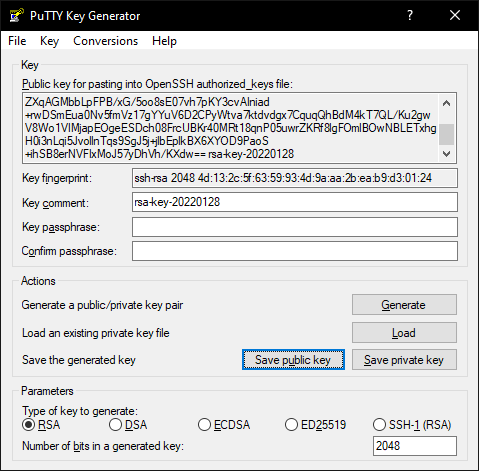
How to Add a Comment to Existing Public and Private Keys (Optional)
You can add comments to a SSH key by typing in a space after the key and putting in the comment. And if you consult the BSD System Manager’s manual, you’ll see that lines starting with # are treated as comments.
How to Assign a Key Passphrase (Optional, but Recommended)
Assigning a key passphrase will enhance the private key’s security by locally encrypting (and decrypting) your private key. You’ll need to enter your key passphrase whenever you connect to your server (the key passphrase acts as another layer of security to connect to your server – almost like 2FA).
How to Upload SSH Public Keys to Your Server
You’ll need to upload the public key to your server after you created the key pair. You can upload the public key through FTP or the server console.
Upload Public Key via FTP
If you want to upload your public key using FTP, start your FTP program and connect to your server as root. Create the following directory in the root-directory:
.ssh
Now create the authorized_keys text file in this folder and paste the whole public key into it. Now save the file.
Upload Public Key via Console
Log yourself in via SSH as root. With this command you can create the right directory and switch to it at the same time:mkdir /root/.ssh && cd /root/.ssh
Now create and open the authorized_keys text file with this command:nano authorized_keys
Paste in your whole public key and save the file by pressing [CTRL+O]. To exit the editor use [CTRL+X]
How to Use Your SSH Private Key with PuTTY:
After you’ve created a key pair consisting of a private key and a public key and after uploading your public key to your server you need to insert your private key into PuTTY.
To do so open PuTTY.
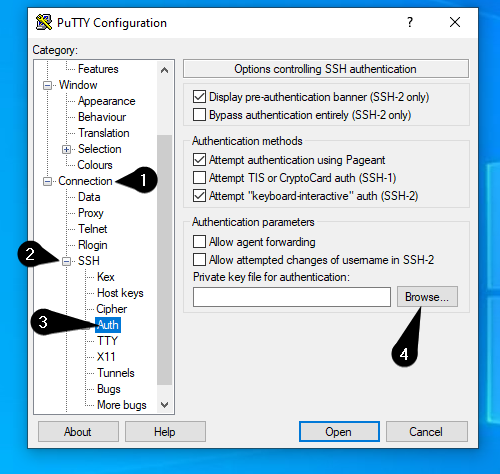
Under “Category” on the left-hand side, you’ll find a list of categories like “Window” and “Connection. Follow these four steps to select your private key:
1: Click “Connection” to expand.
2: Click “[+]” next to “SSH”.
3: Click “Auth” to open a window on the right-hand side
4: Click “Browse” to select your private key
Now scroll up on the left list and click on Session.
Enter your server’s IP-Address and choose a profile name in the Saved Sessions field.
Save your profile by clicking on the Save-Button.
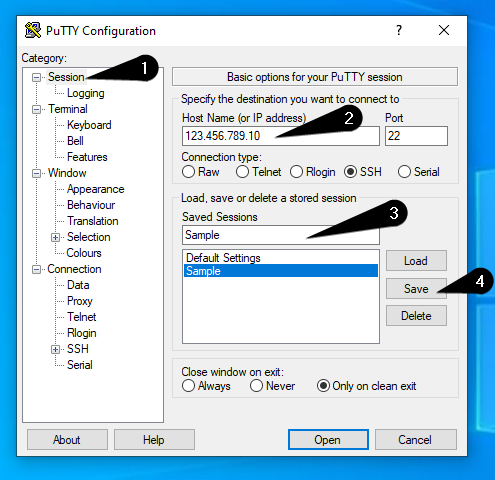
Now you’ve created a profile in PuTTY with your private key.
How to use your SSH Private Key with Pageant:
Alternative to inserting your Private Key into PuTTY you can use Pageant.
Pageant is an SSH-Agent, which comes with PuTTY.
With this program it’s even easier to use Private Keys to connect to your server.
If you use Pageant you don’t need to type in your Passphrase over and over again, in case you secured your Private Key with a Passphrase.
To get started, search for Pageant in the Windows Search Bar. After executing this program, it will appear in the Windows Systemtray:
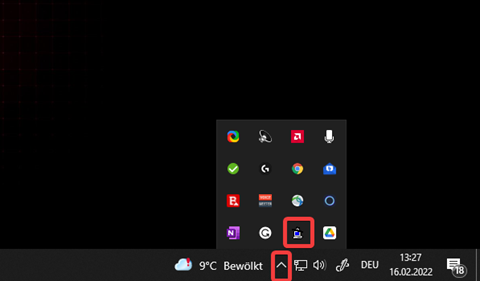
To import a Private Key into Pageant, right-click the Pagent-Icon and click on “Add Key”.
The file explorer will open and you need to select your Private Key. If you decided to secure your Private Key with a Passphrase, you will be asked to enter it.
Now you can just login to your Server without getting prompted to enter your Passphrase everytime you start an SSH connection.
Note: You need to import your Private Key again after rebooting your local computer.
Testing SSH Key Authentication and Disabling Password Authentication:
After you’ve successfully generated a key-pair, uploaded your public-key on the server and created a PuTTY-Profile with your private-key it’s now time to test if your new login method is working.
Testing SSH Key Authentication
To test if your new authentication method is working just login to your server using the PuTTY profile you’ve just created. After double-clicking on the profile, a console will open prompting you to enter your username which is usually root.
After entering the username and confirming it by pressing [Enter] you will be logged in. Besides that, the following message will appear during the login process: “Authenticating with public key <key comment>”.
Disabling Password Authentication
The reason behind choosing ssh-key authentication as your login method is server security. Therefore, it’s logical to disable password authentication now.
To do so open the sshd_config with this command:nano /etc/ssh/sshd_config
Now set the following values to “no”:
ChallengeResponseAuthentication
PasswordAuthentication
UsePAM
To avoid scrolling through the whole config to find the values that need to be changed you can open a search-field by pressing [CTRL+W]. Enter the name of the value and press enter.
If it happens that some values are commented out by a # in front of it, just remove it.
Save your changes with [CTRL+O] and close the editor with [CTRL+X]
Removing SSH Key Authentication and Re-enabling Password Authentication:
If you want to go back to password authentication all you need to do is setting the values in the sshd_config back to “yes”.
After this delete the .ssh folder and its content with:rm -R /root/.ssh
Restart the ssh service with this command:systemctl restart ssh
